Canada's Spy Agency Names Iranian Hacking Group But Omits the DOJ Case That Exposed Its Cartel Bounty on a Canadian Politician
CSIS 2025 public report names the Iranian-linked group Handala Hack for doxxing a journalist while omitting the FBI affidavit attributing the same network to a $250K CJNG bounty on Ghamari.
OTTAWA/WASHINGTON — Canada’s intelligence service has, for the first time, named the Iranian-linked cyber operator at the center of a U.S. federal criminal case that exposed Iran’s issuing a $250,000 bounty death threat directing Mexico’s Jalisco New Generation Cartel to behead a high-profile former Ontario politician at her Ottawa home.
However, CSIS’s annual public report identified the group Handala Hack only in connection with the “doxxing” of a Canadian journalist — while, for unexplained reasons, omitting the far more serious case of apparent narco-terrorism involving a nexus between Iran and a Mexican cartel that Canada designated as a terror entity last year.
As The Bureau reported exclusively in March, the U.S. Department of Justice announced the court-authorized seizure of four websites operated by Iran’s Ministry of Intelligence and Security, dismantling a regime-run cyber and psychological operations network that issued the $250,000 bounty death threat against former Ontario Member of Provincial Parliament Goldie Ghamari, along with an identical threat against a Los Angeles-based critic of the Iranian regime.
The Iranian cyber operations also targeted journalists, Jewish communities, Israeli defense personnel, and Iranian dissidents across North America, the U.S. indictment asserted — tracing how Iran’s cyber operations leveraged Canadian internet infrastructure.
CSIS’s 2025 Public Report, published weeks ago, names the “Handala Hack Team” as an Iranian-linked group responsible for hacking and doxxing attacks against journalists based in Canada, including a Canadian resident working for Iran International, whose photos, provincial driver’s license, permanent resident card, and Iranian passport details were released on the internet and social media platforms.
CSIS describes Handala as a “hacktivist” group that claimed to have infiltrated the “systems, servers, and communication infrastructure” of Iran International, a Farsi-language satellite television network. The agency notes that multiple intelligence firms have linked the group to Iranian Intelligence Services.
“Within days of being doxxed, the Canadian resident began receiving hundreds of violent threats, and their family in Iran was harassed by the authorities,” the CSIS report states. “The objective of this harassment — whether in Canada or elsewhere — is to silence these journalists and compel them to stop working for a media outlet that is highly critical of the Government of Iran. CSIS worked with domestic and foreign partners to respond to this incident.”
But nowhere in its public report does the agency connect the Handala Hack Team to the FBI affidavit unsealed in the District of Maryland, which formally attributes the same group to a single Ministry of Intelligence and Security conspiracy that directed CJNG killers to execute named individuals in North America. The affidavit states that the cartel had already been given the home addresses of its targets at the time the $250,000 bounty threat was issued.
What makes this omission harder to explain is what the agency writes in its own transnational repression section, published in the same report.
Under the category of physical intimidation and violence, CSIS explicitly warns that “hostile state actors sometimes hire organized crime groups or proxies” to project their reach into Canada. Elsewhere, the agency’s own assessment states directly that Iran and other hostile foreign actors “will continue to use proxies, such as individuals involved with transnational organized crime networks, to target perceived enemies living in foreign countries, including Canada.”
The reasons for CSIS’s silence on the connection between Iran’s intelligence apparatus and the Jalisco New Generation Cartel are unknown. CSIS acknowledged a number of questions from The Bureau for this story but had not responded by deadline. Any substantive responses will be added to this story with a note.
As The Bureau reported in March, CSIS’s sister agency, the Royal Canadian Mounted Police, appeared to take a position of denying any evidence of public safety threats related to foreign interference on the very same week that the DOJ’s case exposed Iran’s tasking of a Mexican cartel to lethally threaten a high-profile Canadian political figure.
In March, in an interview with CTV News journalist Vassy Kapelos, RCMP Commissioner Mike Duheme was pressed directly on whether foreign-directed activity poses any threat to public safety in Canada. He said his force could not make the connection.
“I’m saying that based on the totality of the files that we have on foreign interference or transnational repression, what we have in our holdings is we have people that are intimidating people, harassing people, but connecting the dots to a foreign entity, regardless of the country, we don’t have that,” Duheme told Kapelos.
For its part, while CSIS has traditionally been reticent to acknowledge that its intelligence operations focus on significant transnational crime threat actors in Canada, its 2025 report did highlight — in a timeline of important events — that in February 2025, under sustained pressure from the Trump Administration to crack down on fentanyl trafficking and terror networks, the Government of Canada listed seven transnational criminal organizations as terrorist entities: the Cártel del Golfo, the Cártel de Sinaloa, La Familia Michoacana, Cárteles Unidos, La Mara Salvatrucha, Tren de Aragua, and the Cártel de Jalisco Nueva Generación.
The last of those is the same organization that the FBI affidavit identifies as the cartel contracted by Iran’s Ministry of Intelligence and Security to execute Ghamari at her Ottawa home. Under Canada’s security intelligence mandate, CSIS is authorized to investigate activities that constitute a threat to the security of Canada — a mandate that explicitly encompasses terrorism.
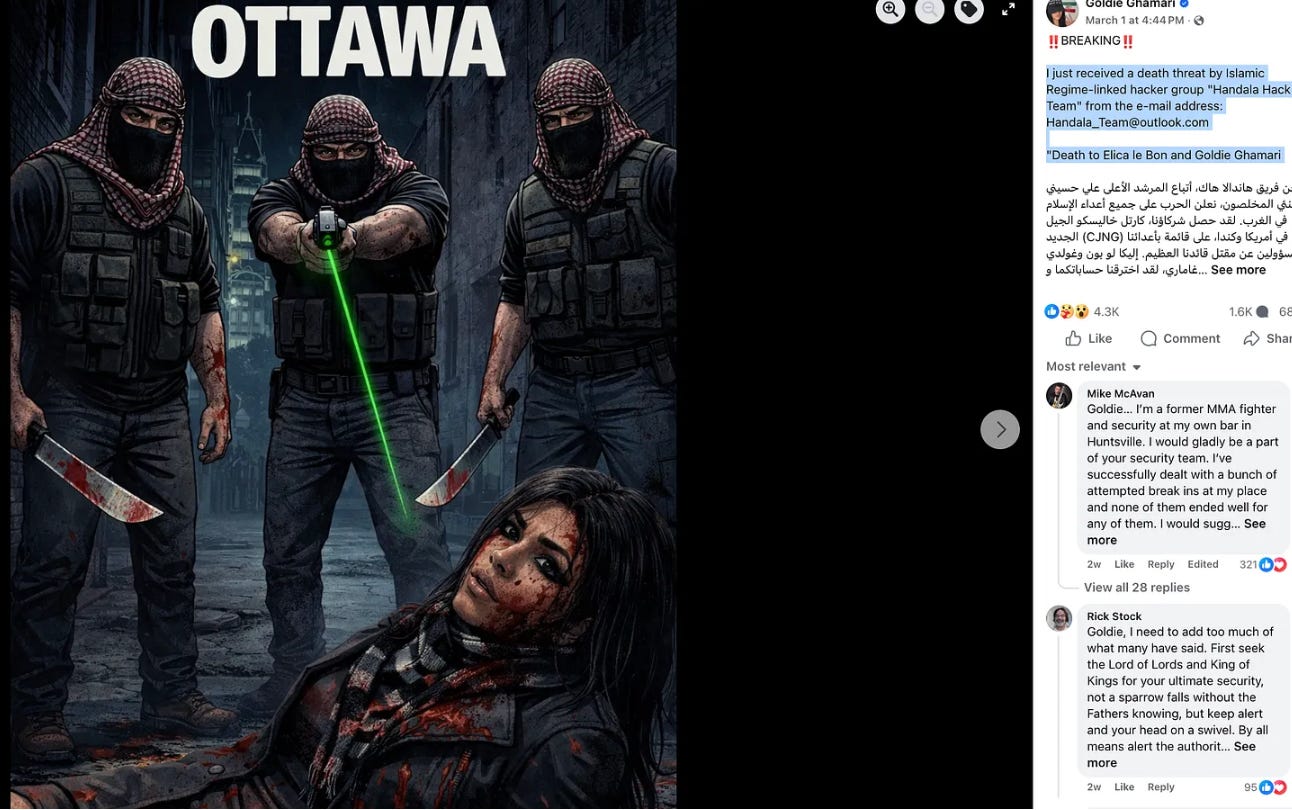
The government’s own February designation placed CJNG within that mandate 13 months before the CSIS annual report was published. Ghamari, on her own Facebook page, reported Handala Hack’s threat including the CJNG bounty, on March 1, 2026. CSIS says it published its annual report in March 2026.
CSIS has not responded yet to a question from The Bureau, asking whether it “is investigating Mexican cartels in relation to narco-trafficking, synthetic lab activities in Canada, and/or connectivity to hybrid threats such as the case … in relation to Handala Hack, or any other hostile state actors inclusive of China or Iran.”
Organized Crime Proxies
The report names Iran as one of five main perpetrators of foreign interference and espionage against Canada — a list led, as in prior years, by the People’s Republic of China, followed by India, the Russian Federation, and Pakistan.
Iran’s return to explicit prominence in CSIS’s public reporting is notable: the agency’s recent public accounts have been dominated by Chinese and Indian interference operations, and Iran’s reappearance reflects what CSIS describes as “shifting geopolitical realities and an increasingly multipolar global environment” in which multiple foreign states and their intelligence services cultivate covert relationships with current and former Canadian politicians, journalists, public servants, academics, and community members.
What the report does not specify is which among those hostile states CSIS assesses as deploying transnational organized crime networks as proxies — even as the agency warns elsewhere in the same document that hostile state actors “sometimes hire organized crime groups or proxies” to project their reach across Canada’s borders.
The People’s Republic of China remains Canada’s pre-eminent intelligence adversary, and the 2025 report documents an evolution in Chinese tradecraft.
In 2025, both the civilian and military arms of PRC intelligence began posting job advertisements through cover companies on mainstream online job marketing sites, targeting Canadians with access to proprietary or classified information.
The CSIS report also points vaguely to a significant threat in this area.
“An espionage alert was released on a PRC intelligence services-affiliated individual targeting Canada’s academic research community to disrupt the threat posed by this individual.”
Alongside that Chinese intelligence recruitment evolution, the report addresses a significant cyber threat. Salt Typhoon, a PRC-linked cyber actor, is assessed to have targeted Canadian telecommunications firms in 2025, potentially compromising customer communications data — including call and text message records.
CSIS notes that Salt Typhoon has already “compromised major telecommunication companies in the US and in other countries” and warns that “similar breaches could occur in Canada,” placing Canadians’ phone calls and text messages at risk of being accessed by hostile actors.
In August 2025, 25 intelligence services, including CSIS, issued a joint cybersecurity advisory documenting that, since 2021, Salt Typhoon has targeted networks globally across telecommunications, government, transportation, lodging, and military infrastructure. CSIS says it continues to investigate and reduce the threat in concert with the Canadian Centre for Cyber Security, and assesses that Salt Typhoon “will remain a concern.”
Editor’s Note: This story was updated to note the timeline of Canada’s designation of CJNG in February 2025, Ghamari’s publicizing Handala Hack’s threat on March 1, 2026, and publication of CSIS’s report, in March 2026.


"....but connecting the dots to a foreign entity, regardless of the country, we don’t have that,” Duheme told Kapelos."
I can't help but wonder, is that because they are not looking for those connections, or they don't want to admit that CSIS relies on the DOJ to feed them this info??
Now that Canada officially is cooperating with China’s police I truly feel secure.🤦♀️ I’d love to know the dirt that the U.S has on our government.